Last Updated: Feb 2025 (Genetic Engineering)
Genetic Engineering
This article deals with ‘Genetic Engineering – UPSC.’ This is part of our series on ‘Science and Technology’ which is an important pillar of the GS-3 syllabus. For more articles, you can click here.
Introduction
- The term ‘Genetic Engineering’ was coined in 1951 by Jack Williamson.
- It is the process of direct human manipulation of the organism’s genome.
- It involves introducing the foreign DNA into the organism of interest to add one or more traits that aren’t found naturally in the organism.
- The organism thus produced is known as GMO or Transgenic organism.
Timeline
| 1960 | Restriction Enzyme was discovered, which could slice the organism’s DNA strand at a particular point. |
| 1973 | Stanley Cohen and Herbert Boyer made the first Genetically Modified Bacteria by successfully removing a particular gene from a bacterium and placing it in another bacterium using the enzyme mentioned above. The organism thus formed is known as a Genetically Modified Organism (GMO). |
| 1974 | Genetically modified Mice was made. |
| 1982 | Insulin-producing Bacteria was commercialized. |
| 1982 | The Antibiotic-Resistant Tobacco plant, which was the first genetically modified crop, was produced. |
| 1994 | Genetically Modified Food has been sold since 1994. |
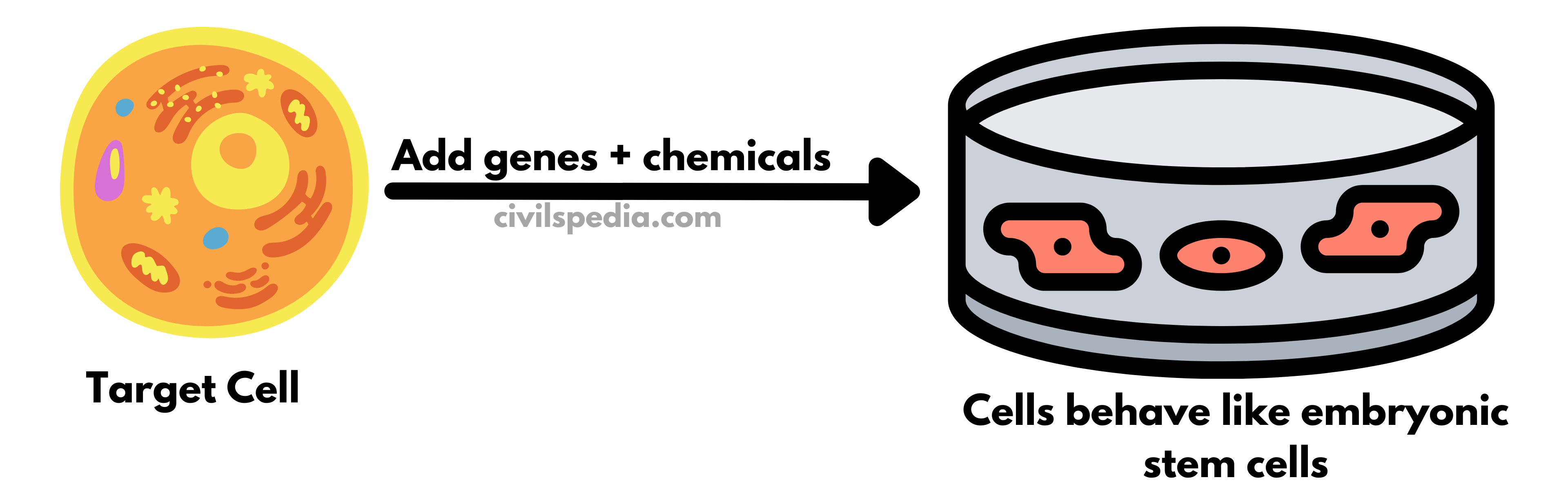
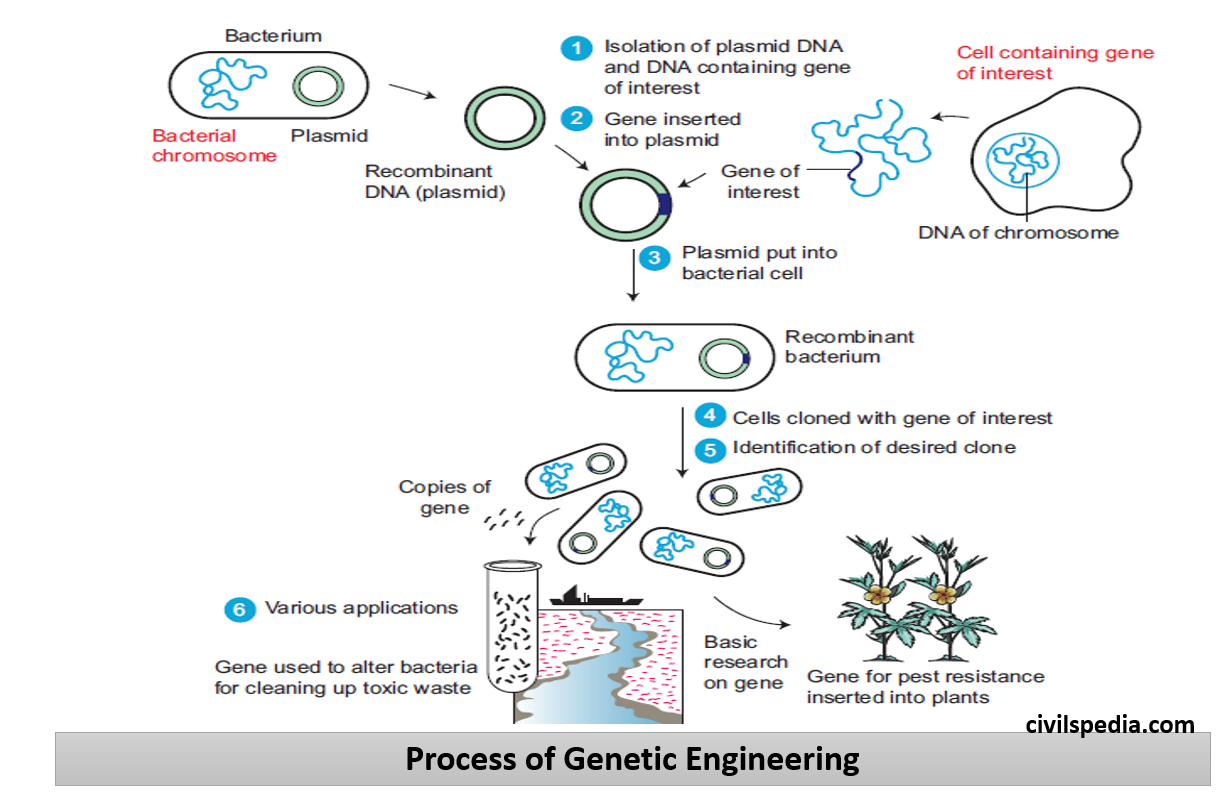
Method of Genetic Engineering
- Genome is relatively resistant to change. To deter any changes from being inadvertently made to DNA, cells have inherent mechanisms to proofread and repair their genetic code. Remarkably, researchers have taken advantage of the cell’s DNA repair mechanisms to achieve genome editing.
- To accomplish this, scientists can use
- Artificially engineered enzymes called Nucleases act as molecular scissors and are used to crack open DNA strands.
- Once the break is introduced in DNA, the cell will detect the problem & quickly activate repair machinery.
- DNA sequence designed to be inserted is also sent along with a Nuclease, such that when a cut is made in the DNA, the cell’s own repair mechanism can use the DNA sequence supplied to replace an existing DNA sequence.
- This method allows scientists to change the genetic makeup of cells directly.
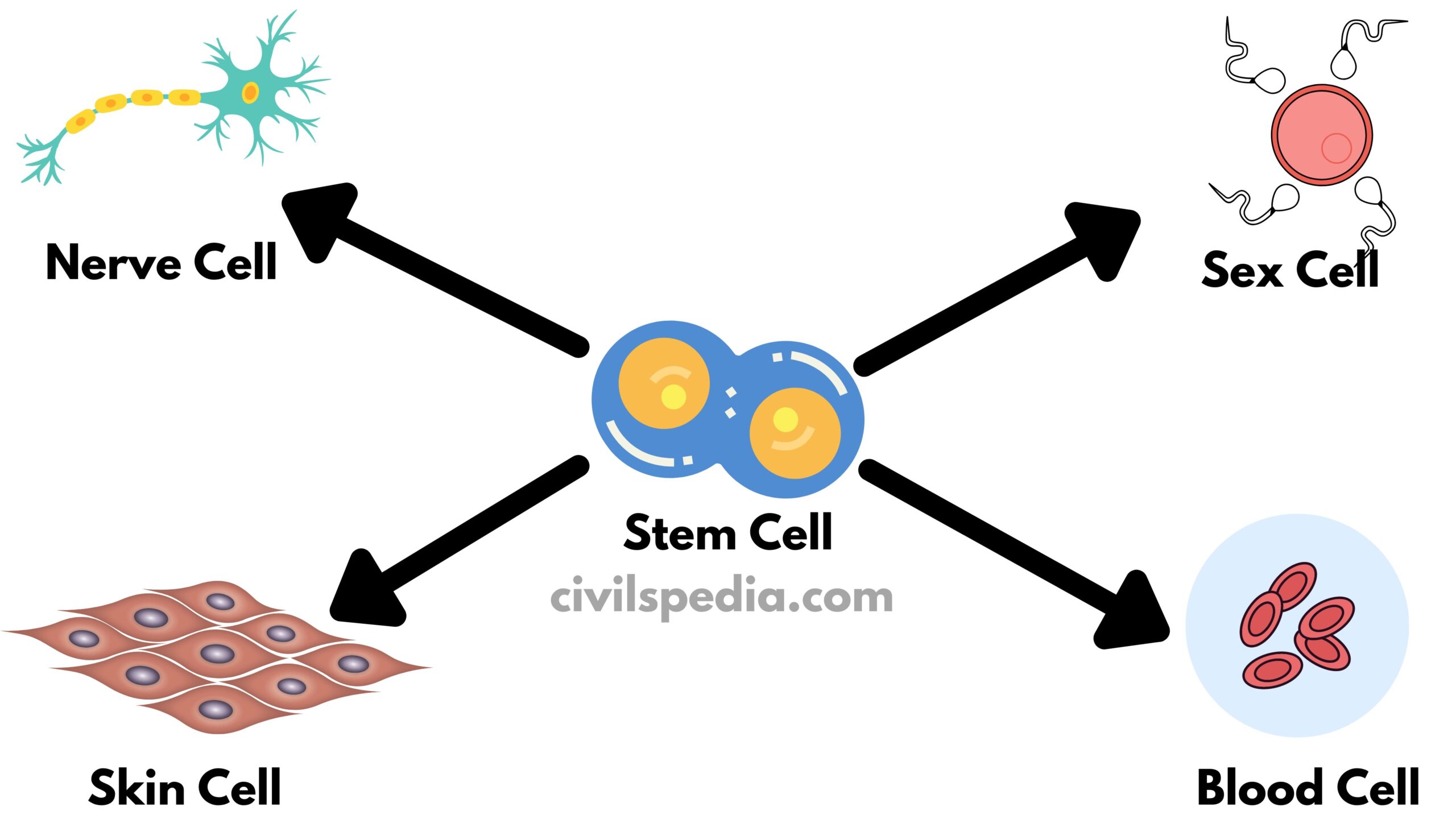
Type of Genetically Modified Organisms (GMOs)
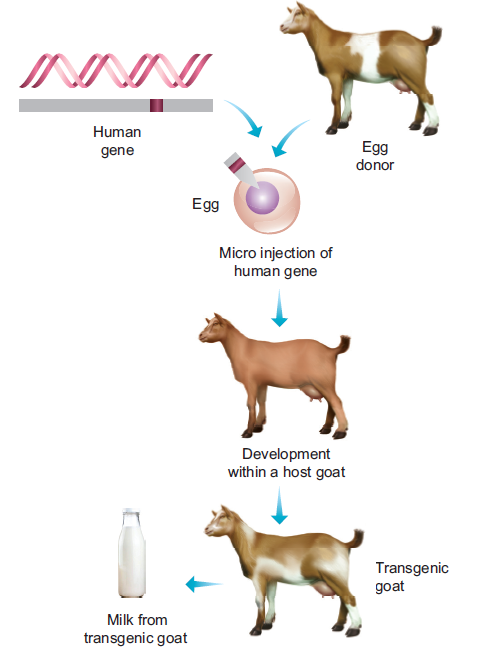
Genetic material can be inserted from the same species as well as other species. Accordingly, they are known as Transgenic and Cisgenic GMOs.
| Transgenic | Genetic material from the other species is added to the host. |
| Cisgenic | Genetic material from the same species or one that can be naturally bred with is added to the host. |
Applications of Genetic Engineering

1 . Human Medicine
- Insulin: Insulin is obtained from genetically engineered E. Coli, which is pure and cheaper than earlier sources, i.e. pancreas of abattoir animals. It was the first-ever genetically engineered biopharma product released on the market. (Note: Insulin controls the glucose levels in the body, and its deficiency results in diabetes.)
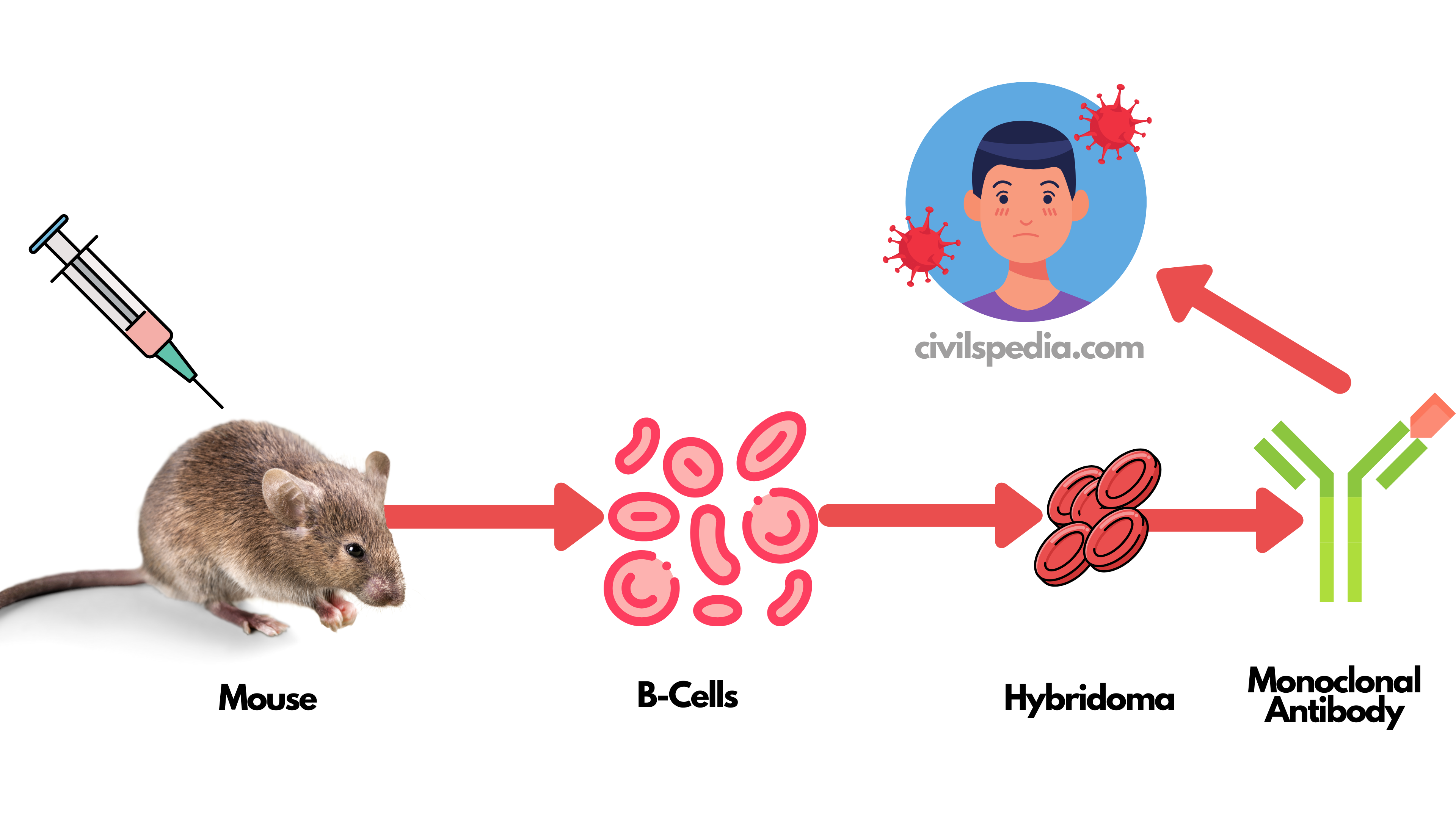
- Recombinant Vaccines: These are new generations of vaccines. They are pure and have lesser side effects compared to conventional vaccines.
- Edible Vaccines: An edible vaccine is derived through the genetically engineered expression of an antigenic protein by an edible plant. They have the advantage over animal-derived vaccines such as easy bulk production and stability at room temperature.
- Recombinant Blood Clotting Factor VIII: This helps in curing the patients who have haemophilia. In haemophilia person’s body produces a lesser amount of Factor VIII, which helps the body in blood coagulation.
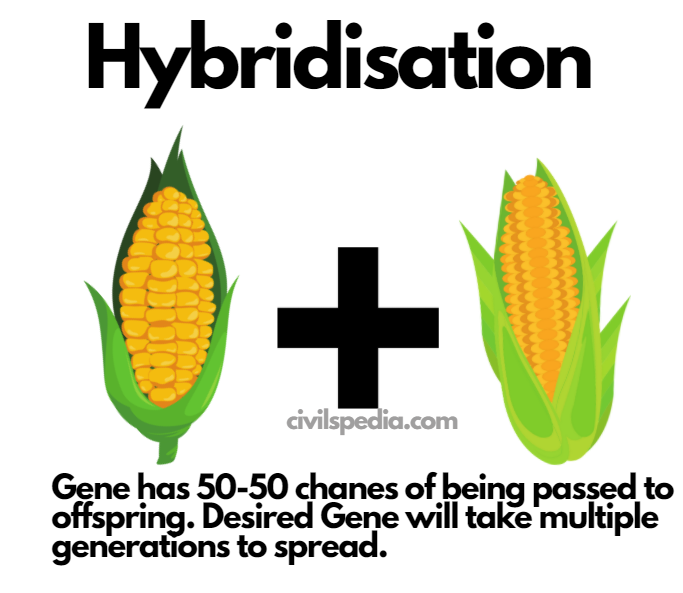
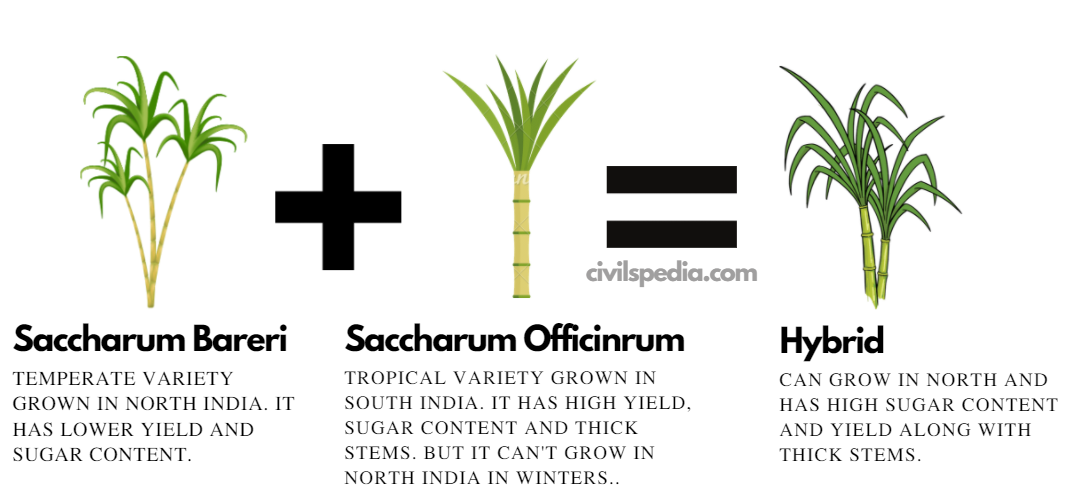
2. Genetically Modified Crops
- Genetic Engineering is used to produce GM crops with desirable characteristics such as
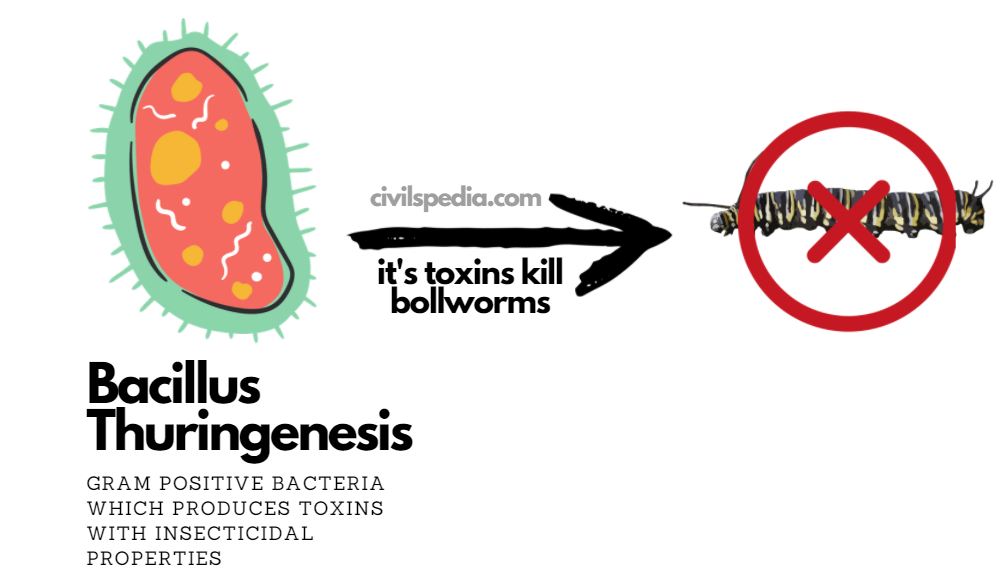
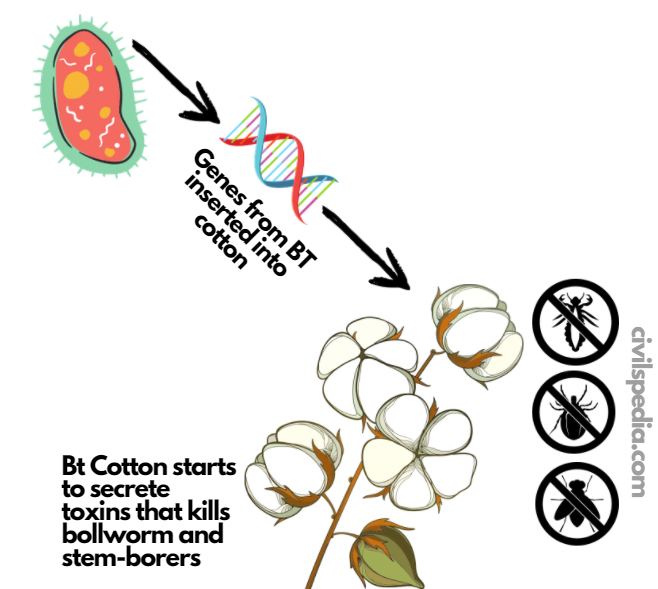
- Pest, Virus & Drought-Resistant varieties such as BT Cotton (having pesticidal properties that are non-toxic to mammals) & virus-resistant GM Papaya grown in Hawaii.
- Weed Control: Scientists have integrated a recombinant gene in the crops that cause resistance to the herbicide glyphosate and simplifies weed control by glyphosate application.
- Slow ripening
- Better nutritional value like Golden Rice (with biofortified Vitamin A (Beta Carotene)).
3. Improved Animal Breeds
- Like transgenic fish was made to grow rapidly by insertion of the growth hormone gene.
4. Enhancement Genetic Engineering/ Eugenic / Designer Babies
- It involves the insertion of a gene to enhance the specific character like growth hormone or intelligence etc., for enhanced growth or intelligence than ordinary children.
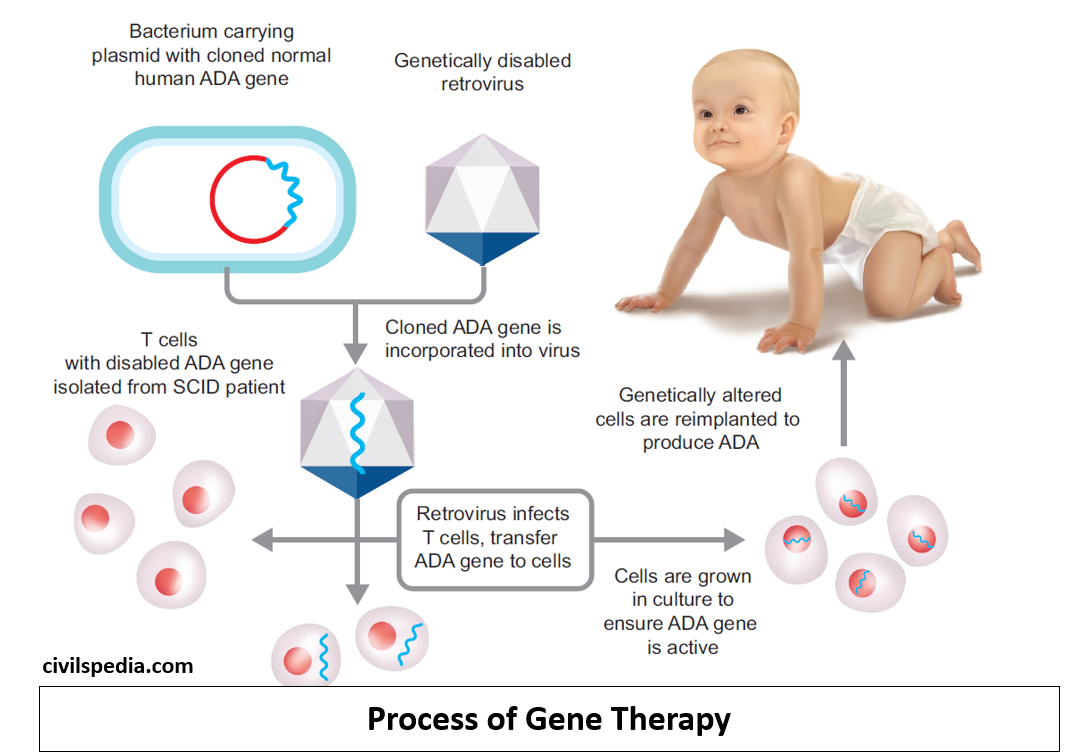
5. Gene Therapy
- Using gene manipulating techniques to treat genetic diseases by replacing defective genes with healthy genes or bolstering the body’s immunity.
6. Gene Doping
- The misuse of gene editing in which athletes resort to gene editing to increase their physical stamina. According to WADA (World Anti-Doping Agency), Gene Doping is a hazard to a sport’s integrity and athlete’s health.
7. Environmental Remediation
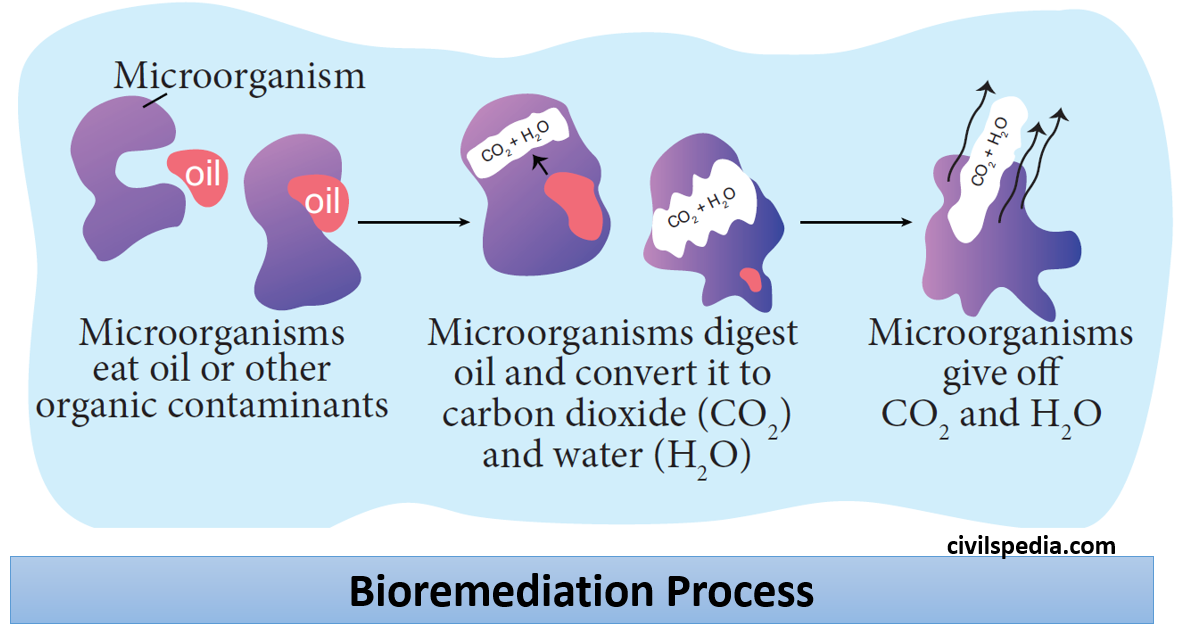
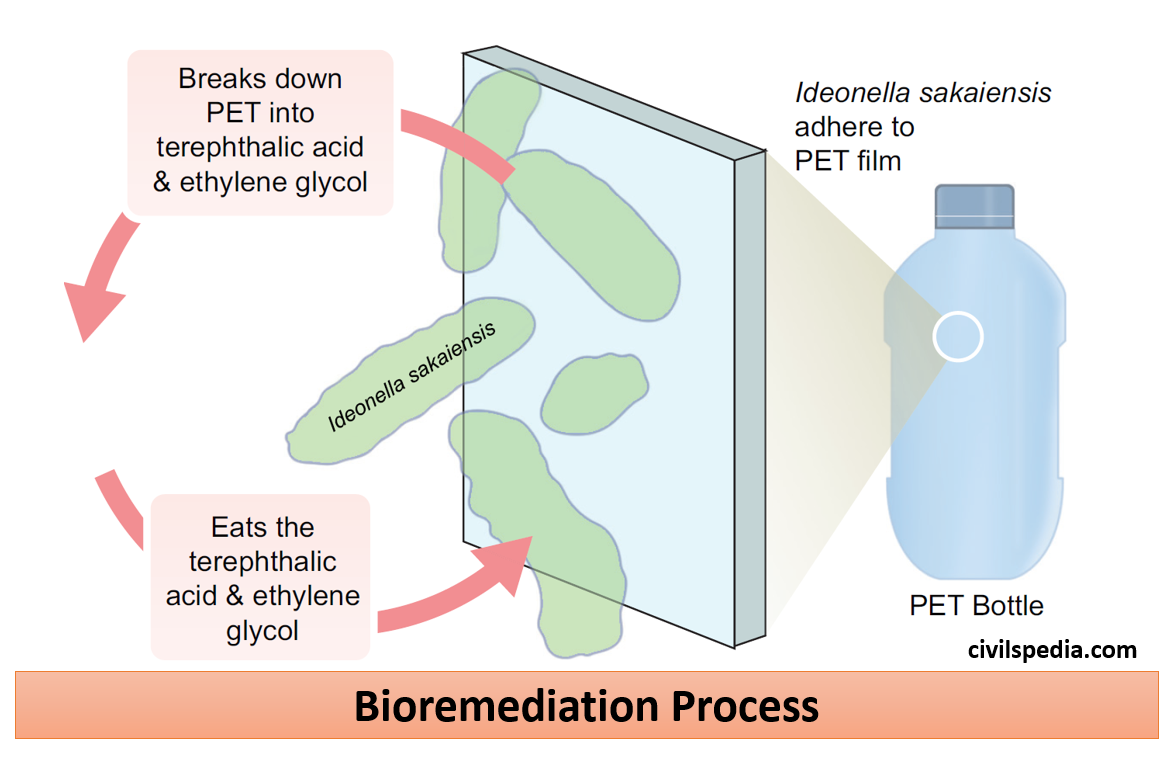
- Genetically modified organisms are being used to clean up polluted sites. Examples include Pseudomonas Putida (a GM organism that is used to clean oil spills. This is patented by Ananda Mohan Chakrabarty).
Concerns with Genetic Engineering
1. Gene Delivery Tools
- Genes are inserted into the body using vectors which are usually viruses.
- Viruses can produce other problems like
- Toxicity
- Immune response
- Inflammatory response
- Gene control and targeting issues
2. High Costs / Equity Concerns
- The whole process is quite expensive and hence not inclusive. It will create the division in society between haves and have-nots.
3. Ethical Dilemma
- Principal concerns include morality, eugenics helping the fittest to survive, ongoing clinical debates about informed consent, religious debate, the possible rise of clones, designer babies, and possibly super-humans.
4. Informed Consent
- In the case of germline therapy, it is impossible to obtain informed consent as the patients affected by the editing are the embryo and future generations.
5. Limited Knowledge of the Functions of the Genes
Scientists know functions of limited genes, and worst is in some cases, scientists don’t know whether a particular gene is performing more than one function
6. Regulatory Concerns
Developing appropriate regulations and guidelines to govern the use of genome editing technologies presents a challenge to ensure responsible and safe applications
7. Others
- It might lead to designer babies & the commodification of children.
- It can be used in biological warfare.
- Recreation of extinct species can lead to disasters.
- If a wrong DNA segment is inserted and if it gets expressed, it can cause new diseases in human beings.
Side Topic: Gene Knock Out
A gene ‘knock out’ is a genetically engineered organism that carries one or more genes in its chromosomes that have been made inoperative.
CRISPR-Cas9
Currently, four families of engineered nucleases (Molecular Scissor) are used:
- Mega Nucleases
- Zinc Finger Nucleases
- Transcription Activator like Effector based Nucleases (TALENs)
- CRISPR- Cas System (Most advanced & important)
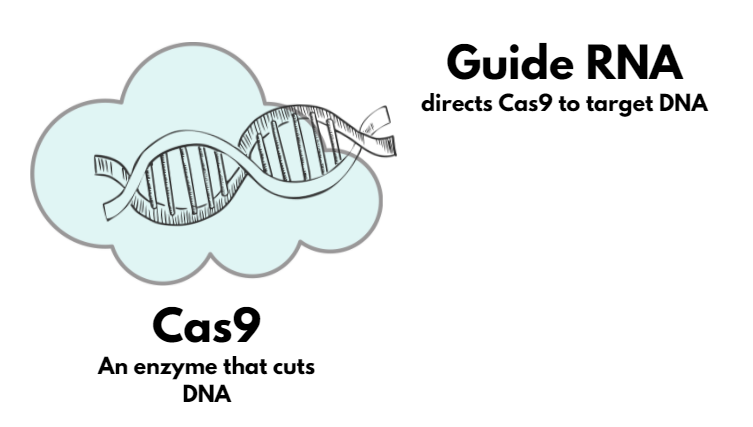
CRISPR/Cas9 System of Germline Editing
- CRISPR Cas 9 technology works like a cut-and-paste mechanism on DNA strands. The DNA strand identifies the specific location of the genetic codes that need to be changed or “edited” and then, using the Cas9 protein, which acts like a pair of scissors, that location is cut off from the strand. Once the DNA strand is broken, it has a natural tendency to repair itself. During the auto-repair process, Scientists intervene by supplying the desired sequence of genetic codes that binds with the broken DNA strand.
- Nobel Prize for Chemistry in 2020 was awarded for discovering the CRISPR Cas9 scissor.
- It is a revolutionary technique for Gene Editing with very high efficacy
- CRISPR: It is the mechanism that Bacteria uses to protect themselves from viruses. In this system, DNA is plucked out of Virus and inserted in little bits into the bacterium’s chromosome. In this way, Bacteria records the viruses it has been exposed to so that cells are protected from those viruses in the future.
- Cas 9 is a cutting enzyme.
Stage 1
Guide RNA is shepherded with Cas 9 System
- RNA is used to guide Cas 9 to the targeted position.
- Cas 9 is used to make a cut.
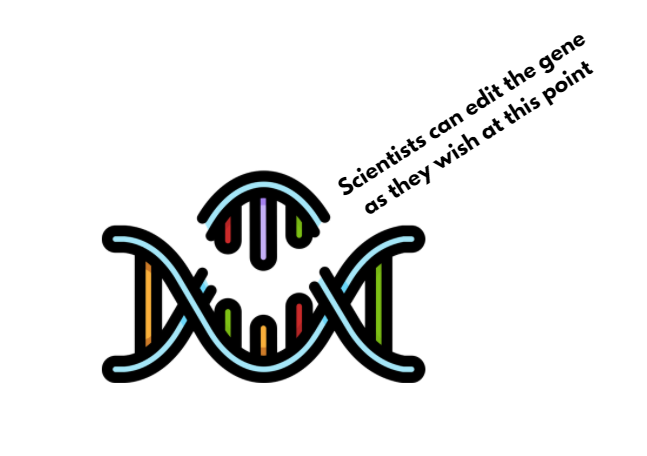
Stage 2
- Cas 9 locks onto DNA &
unzips it (both strands are divided).
Stage 3
- Cas 9 snips the DNA, creating a break in both strands.
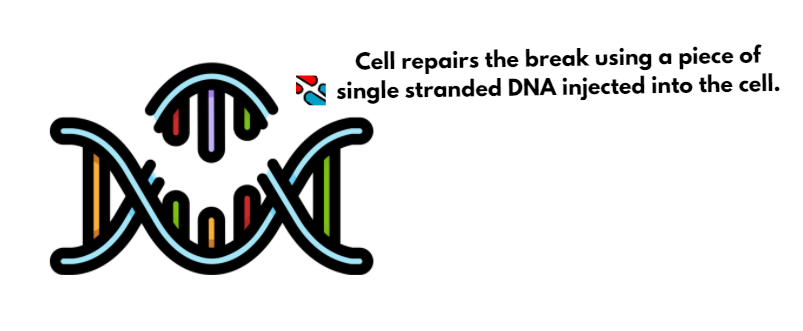
Stage 4
- The DNA will repair itself using an inbuilt repaid mechanism using a piece of single-stranded DNA injected into the cell that binds itself with the broken DNA strand.
Why it is revolutionary
- It is cheaper (than already existing gene-editing technology).
- It has very high efficacy.
Uses/ Applications
Its applications are immense, and it has made the designer baby a reality. Since it will have a wide range of ethical and social implications, inventors Jennifer Doudna and Emmanuelle Charpentier have called for Moratorium until proper consensus on its use is made.
- Cure to diseases: CRISPR Cas-9 technology is used to treat many incurable diseases. It includes the cure for Sickle Cell Anaemia, diabetes, inherited eye diseases, and various types of cancers. E.g., in 2023, the US has approved CRIPR based gene therapies (named Casgevy and Lyfgenia) to treat patient with Sickle Cell Disease. Additionally, clinical trials are going on to treat diseases like HIV/AIDS, diabetes, cancer etc.
- Controlling number of mosquitos: Scientists have used the CRISPR technique to produce sterile male mosquitos of species that are responsible for spreading diseases such as malaria, dengue, zika etc.
- Some scientists call for bringing extinct species back to life using this technology, like the Oxford Universities project on reviving Mammoth.
Issues with the Technology
- Designer Babies: Bioethicists fear abuse of gene editing by the private sector, preying on a parent’s desire to create a perfect child. In 2018, a Chinese researcher disclosed that he had altered the genes of a human embryo to prevent the infection of HIV. It was the first documented case of creating a ‘designer baby’, and it caused widespread concern in the scientific community.
- Issue of Informed Consent: Bioethicists have also raised the concern that it is impossible to obtain up-to-date consent for germline therapy because the patients affected by the edits are the embryo and future generations.
- Inclusivity Issue: Only wealthy people will be able to afford this technology, increasing existing disparities and creating another class of haves and have-nots.
- OffTarget Effects: CRISPR Cas9 can sometimes edit unintended locations in the genome, leading to potential genetic alterations with unknown consequences.